Installing VPN access on Windows Server 2016
-
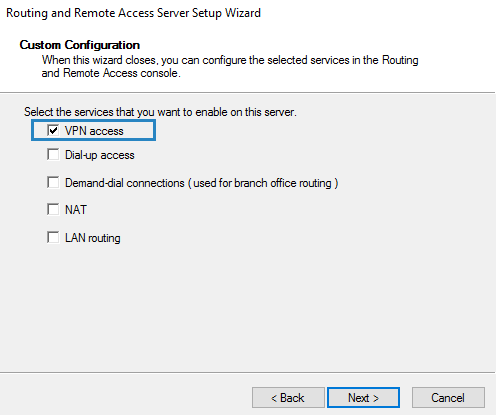
A Virtual Private Network connection allows creating a secure connection over shared or public networks, such as the Internet, to a private network at a remote location. VPN can be installed on Windows Server 2016 to protect the network and remote connection from attacks or data sniffing via tunneling protocols inside of a standard data connection.
Read the full article by Vladan Seget, IT and Virtualization consultant to learn how to deploy Remote Access VPN on Windows Server 2016.
-
I've never seen much love for Windows VPN. Best practice seems to be to install a VPN on your firewall instead. Is that still the case? If so, why? I already expose other Windows servers/ports to the internet (e.g. Exchange, IIS).
-
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
I've never seen much love for Windows VPN. Best practice seems to be to install a VPN on your firewall instead. Is that still the case? If so, why? I already expose other Windows servers/ports to the internet (e.g. Exchange, IIS).
Some people don't like exposing those ports either.. instead they rather expose a reverse proxy in front of them.
-
Dash is correct, the general thinking in many cases is that you put a VPN aggregator at the edge and expose nothing else, only that. I'm not saying that's some magic answer, but it is the "LAN Security Model" that is why VPNs were really created.
-
Why?
E.g. How does a reverse proxy make Exchange more secure? Or to put it another way, what are the Exchange security flaws that you're trying to fix?
-
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Why?
E.g. How does a reverse proxy make Exchange more secure? Or to put it another way, what are the Exchange security flaws that you're trying to fix?
Why - the only answer I can give is - because. that's way it's pretty much always been done. As Scott inferred, it's likely not needed. Besides - why do you still have onsite Exchange?

-
That's the way it's always been done?
Years ago, it was generally accepted that Microsoft products weren't very secure and that you wouldn't want to expose them. But it's 2017 now, and I'm not sure that assumption still applies.
People used to explain it to me by saying "cuz it's Microsoft, duh..". Now I need to know specifics on how an attack on an exposed MS product could play out and why.
I'm only using Exchange as an example, I'm also interested in Window VPN and IIS.
-
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
That's the way it's always been done?
Years ago, it was generally accepted that Microsoft products weren't very secure and that you wouldn't want to expose them. But it's 2017 now, and I'm not sure that assumption still applies.
The assumption isn't one that Windows is less secure than any linux distribution, its' that there is far more threats for Windows in existence that makes leaving a Windows server open (or any ports) to great of a risk.
-
Can you give me some examples?
-
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Why?
E.g. How does a reverse proxy make Exchange more secure? Or to put it another way, what are the Exchange security flaws that you're trying to fix?
Reverse proxy does very little, but it does make direct brute force attacks go against the proxy rather than the email server. The hope is that it will "fail closed" rather than "fail open" .
-
@DustinB3403 said in Installing VPN access on Windows Server 2016:
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
That's the way it's always been done?
Years ago, it was generally accepted that Microsoft products weren't very secure and that you wouldn't want to expose them. But it's 2017 now, and I'm not sure that assumption still applies.
The assumption isn't one that Windows is less secure than any linux distribution, its' that there is far more threats for Windows in existence that makes leaving a Windows server open (or any ports) to great of a risk.
I think it is often product by product. Exchange is designed to have layers of security like this, that's the intended use. RDP they assume you will layer some other security in front of, etc.
-
@Dashrender said in Installing VPN access on Windows Server 2016:
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Why?
E.g. How does a reverse proxy make Exchange more secure? Or to put it another way, what are the Exchange security flaws that you're trying to fix?
Why - the only answer I can give is - because. that's way it's pretty much always been done. As Scott inferred, it's likely not needed. Besides - why do you still have onsite Exchange?

That's the biggest answer. Just because "it's what people do."
-
Exchange is (now) designed to be exposed. So it's hardened and is secure. Or if it isn't, I'd like someone to explain why it isn't and how I should protect it.
So to return to the OP, Windows VPN is designed to be exposed, right? It's designed to be secure, right? So why not use it? What are it's flaws? Unlike years ago, Microsoft develop products with security at the fore.
-
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Exchange is (now) designed to be exposed. So it's hardened and is secure. Or if it isn't, I'd like someone to explain why it isn't and how I should protect it.
Is that true? MS has made a point of making a lot of layers of Exchange and good design is normally assumed to have a SPAM filter in front of it so that Exchange itself is never really exposed. Exchange being "designed" to be exposed would imply a flaw in thinking from MS, but I don't think that they've made that mistake. Exchange is still designed or intended to be used in a good email architecture.
-
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Exchange is (now) designed to be exposed. So it's hardened and is secure. Or if it isn't, I'd like someone to explain why it isn't and how I should protect it.
So to return to the OP, Windows VPN is designed to be exposed, right? It's designed to be secure, right? So why not use it? What are it's flaws? Unlike years ago, Microsoft develop products with security at the fore.
There are products that don't require you to pay a small fortune to be able to VPN in. Maybe that's why people don't use Windows VPN.
That and it's still a Windows Server (so even if it is hardened) it's still vulnerable to everything bad out there.
-
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
So to return to the OP, Windows VPN is designed to be exposed, right?
I'm not sure that I like these terms "designed to be". I understand where you are coming from, but let's ask about something totally different...
Is a Node.js server "designed to be" exposed without a proxy in front of it?
Or, is Windows Software RAID "designed to be" used for your storage?
-
@scottalanmiller said in Installing VPN access on Windows Server 2016:
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Exchange is (now) designed to be exposed. So it's hardened and is secure. Or if it isn't, I'd like someone to explain why it isn't and how I should protect it.
Is that true? MS has made a point of making a lot of layers of Exchange and good design is normally assumed to have a SPAM filter in front of it so that Exchange itself is never really exposed. Exchange being "designed" to be exposed would imply a flaw in thinking from MS, but I don't think that they've made that mistake. Exchange is still designed or intended to be used in a good email architecture.
And what is good Email architecture?
-
@Dashrender said in Installing VPN access on Windows Server 2016:
@scottalanmiller said in Installing VPN access on Windows Server 2016:
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Exchange is (now) designed to be exposed. So it's hardened and is secure. Or if it isn't, I'd like someone to explain why it isn't and how I should protect it.
Is that true? MS has made a point of making a lot of layers of Exchange and good design is normally assumed to have a SPAM filter in front of it so that Exchange itself is never really exposed. Exchange being "designed" to be exposed would imply a flaw in thinking from MS, but I don't think that they've made that mistake. Exchange is still designed or intended to be used in a good email architecture.
And what is good Email architecture?
Having a spam filter in front, and often a smart host for outgoing, and an edge device to handle the MTA tasks in front of the mailbox unit. All stuff that MS preaches.
-
@scottalanmiller said in Installing VPN access on Windows Server 2016:
@Dashrender said in Installing VPN access on Windows Server 2016:
@scottalanmiller said in Installing VPN access on Windows Server 2016:
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Exchange is (now) designed to be exposed. So it's hardened and is secure. Or if it isn't, I'd like someone to explain why it isn't and how I should protect it.
Is that true? MS has made a point of making a lot of layers of Exchange and good design is normally assumed to have a SPAM filter in front of it so that Exchange itself is never really exposed. Exchange being "designed" to be exposed would imply a flaw in thinking from MS, but I don't think that they've made that mistake. Exchange is still designed or intended to be used in a good email architecture.
And what is good Email architecture?
Having a spam filter in front, and often a smart host for outgoing, and an edge device to handle the MTA tasks in front of the mailbox unit. All stuff that MS preaches.
I'm curious, does MS have non Exchange hosts acting as a spam filter for O365?
-
@scottalanmiller said in Installing VPN access on Windows Server 2016:
@Dashrender said in Installing VPN access on Windows Server 2016:
@scottalanmiller said in Installing VPN access on Windows Server 2016:
@Carnival-Boy said in Installing VPN access on Windows Server 2016:
Exchange is (now) designed to be exposed. So it's hardened and is secure. Or if it isn't, I'd like someone to explain why it isn't and how I should protect it.
Is that true? MS has made a point of making a lot of layers of Exchange and good design is normally assumed to have a SPAM filter in front of it so that Exchange itself is never really exposed. Exchange being "designed" to be exposed would imply a flaw in thinking from MS, but I don't think that they've made that mistake. Exchange is still designed or intended to be used in a good email architecture.
And what is good Email architecture?
Having a spam filter in front, and often a smart host for outgoing, and an edge device to handle the MTA tasks in front of the mailbox unit. All stuff that MS preaches.
Personally I do use a Spam filter in front of my Exchange Server for email, but skipped the smart host for outgoing.
I also have a reverse proxy in front of Exchange for ActiveSync and OWA.














