[ALERT] New Fileless, Code-injecting Ransomware Bypasses Antivirus
-
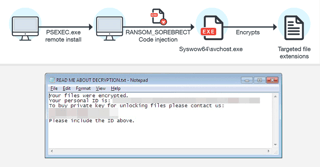 Security researchers have discovered a new fileless ransomware in the wild, which injects malicious code into a legitimate system process (svchost.exe) on a targeted system and then self-destructs itself in order to evade detection by antivirus.
Security researchers have discovered a new fileless ransomware in the wild, which injects malicious code into a legitimate system process (svchost.exe) on a targeted system and then self-destructs itself in order to evade detection by antivirus.The nasty has been called SOREBRECT and unlike more generic "spray-and-pray" ransomware, it has been designed to specifically target enterprise systems in various industries.
SOREBRECT also takes pains to delete the infected system’s event logs and other artifacts that can provide forensic information such as files executed on the system, including their timestamps. These deletions deter analysis and prevent SOREBRECT’s activities from being traced.
This malicious code, after it has taken control of the machine, uses Microsoft’s Sysinternals PsExec command-line utility to encrypt files. I am sure that Mark Russinovich is not happy about this!
Why PsExec?
“PsExec can enable attackers to run remotely executed commands, instead of providing and using an entire interactive login session, or manually transferring the malware into a remote machine, like in RDPs,” Trend Micro says.
SOREBRECT Also Encrypts Network Shares
SOREBRECT also scans the local network for other connected computers with open shares and locks files available on them as well. “If the share has been set up such that anyone connected to it has read-and-write access to it, the share will also be encrypted,” researchers say.
In addition, SOREBRECT uses the Tor network protocol in an attempt to anonymize its communication with its command-and-control (C&C) server, just like almost every other malware.
Sorebrect Ransomware Spreads Worldwide
According to Trend Micro, Sorebrect was initially targeting Middle Eastern countries like Kuwait and Lebanon, but from last month, this threat has started infecting people in Canada, China, Croatia, Italy, Japan, Mexico, Russia, Taiwan, and the U.S.
This is not the first time when researchers have come across Fileless malware. Two months ago, Cisco's Talos researchers discovered a DNSMessenger attack that was completely fileless and used DNS TXT messaging capabilities to compromise systems.
In February, Kaspersky researchers also discovered fileless malware that resided solely in the memory of the compromised computers, which was found targeting banks, telecommunication companies, and government organizations in 40 countries.
Fileless malware is much harder to detect by antivirus than malware that first lies down a file on disk, and then does its dirty work. Kaspersky said: ""Unfortunately the use of common tools combined with different tricks makes detection very hard. In fact, detection of this attack would be possible in RAM, network and registry only."
What To Do About It
Below the best practices for securing your systems and network against SOREBRECT suggested by TrendMicro.
-
Restrict user write permissions
-
Limit privilege for PsExec
-
Back up files
-
Keep the system and network updated
-
Deploy multilayered security mechanisms
-
Foster a cybersecurity-aware workforce.
Trend Micro advised: "User education and awareness helps improve everyone’s security posture. Like other malware, ransomware’s points of entry is typically through email and malicious downloads or domains. Organizations should conduct regular training to ensure that employees have a solid understanding of company security policy, procedure, and best practices."
We could not agree more. You need defense-in-depth and a human firewall as your last line of defense. Here is a free job-aid for your employees. It's a single page with the 22 Social Engineering Red Flags. They can print it and pin it to their wall. This is a link to a PDF that is hosted at HubSpot, where our website lives:
https://cdn2.hubspot.net/hubfs/241394/Knowbe4-May2015-PDF/SocialEngineeringRedFlags.pdf?
Warm regards, Stu
-
-
Although this method of infection isn't new at all (I've played with it during some Webinar/Demo a year ago or something like that), using it with ransomware is the first I've seen!
Thanks for the info!